IMDEA Networks

News
IMDEA Networks participates in the development of the photonic chip of the future
IMDEA Networks is already working on the development of photonic integration technologies that will revolutionize the next generations of communications...
Read more arrow_right_altYour conversations with AI may not be as private as you think
A study conducted by researchers at IMDEA Networks Institute has revealed that ChatGPT (OpenAI), Claude (Anthropic), Grok, and Perplexity AI...
Read more arrow_right_altNEXTONIC marks a landmark 2025: ten years of open innovation and a new chapter toward 6G
2025 has been a milestone year for the open innovation laboratory founded by Telefónica and IMDEA Networks. The laboratory celebrated...
Read more arrow_right_altGuillermo Suárez-Tangil promoted to Research Associate Professor at IMDEA Networks
Guillermo Suárez-Tangil has been promoted to Research Associate Professor at IMDEA Networks Institute, following a rigorous and highly competitive selection...
Read more arrow_right_alt29 students discover the world of research at IMDEA Networks through the 4th ESO+Empresa programme
On 25 and 26 March, IMDEA Networks hosted 29 fourth-year secondary school students as part of the Community of Madrid’s...
Read more arrow_right_altIMDEA Networks at the 15th Edition of the Madrid is Science Fair
Thousands of people visited the IMDEA Networks stand at the Madrid is Science Fair, held from March 19 to 21...
Read more arrow_right_altYour car’s tire sensors could be used to track you
Researchers at IMDEA Networks Institute, together with European partners, have found that tire pressure sensors in modern cars can unintentionally...
Read more arrow_right_altIMDEA Networks researchers recognized as Distinguished Members of IEEE INFOCOM 2026 Technical Program Committee
Researchers from the IMDEA Networks Institute have been recognized as Distinguished Members of the Technical Program Committee (TPC) of IEEE...
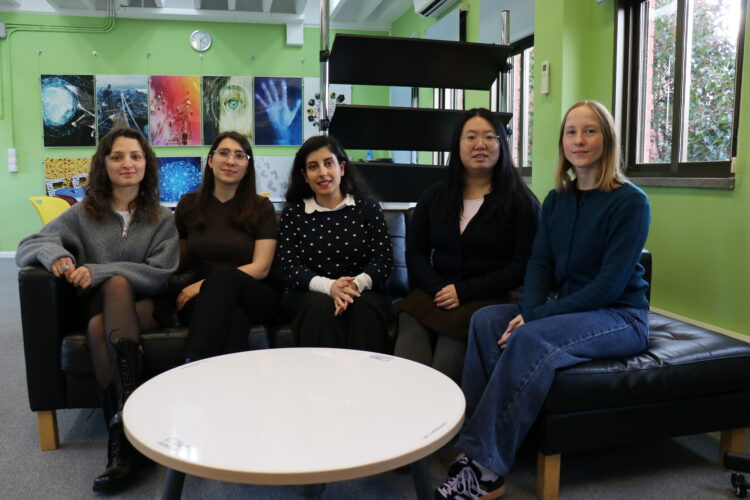
Read more arrow_right_altWomen in STEM: Stories to inspire the next generation
As part of the International Day of Women and Girls in Science, we interviewed five of our researchers to learn...
Read more arrow_right_altIMDEA Networks deploys cutting-edge smart lamppost with 5G millimeter-wave and WiFi 7 technology with NEXTONIC partners
IMDEA Networks Institute has successfully deployed a state-of-the-art smart lamppost at its outdoor facilities in Leganés, Madrid, marking a significant...
Read more arrow_right_alt









Recent Comments