IMDEA Networks

News
IMDEA Networks research on a new AI explainability tool for mobile networks wins award at IEEE INFOCOM 2024
The work “AIChronoLens: Advancing Explainability for Time Series AI Forecasting in Mobile Networks” (by Claudio Fiandrino, Eloy Pérez Gómez, Pablo...
Read more arrow_right_altORIGAMI: anticipating the future of more connected, efficient and sustainable telecommunication infrastructures
The ORIGAMI (Optimized Resource Integration and Global Architecture for Mobile Infrastructure for 6G) project is now underway. The project, funded...
Read more arrow_right_alt20 students carry out an educational internship at IMDEA Networks with the 4ºESO+Enterprise Program
On March 18 and 19, 20 students from IES Isaac Albéniz (Leganés), IES Arquitecto Peridis (Leganés), IES Maestro Matías Bravo...
Read more arrow_right_altIMDEA Networks at the XIII edition of Madrid is Science Fair
Hundreds of people visited the IMDEA Networks stand at the ‘Madrid is Science Fair’ which took place from Thursday, March...
Read more arrow_right_altIMDEA Networks shows its new facilities to authorities from the Community of Madrid, UC3M and Leganés City Hall
IMDEA Networks was visited today by the Regional Minister of Education, Science and Universities Emilio Viciana, the Regional Minister of...
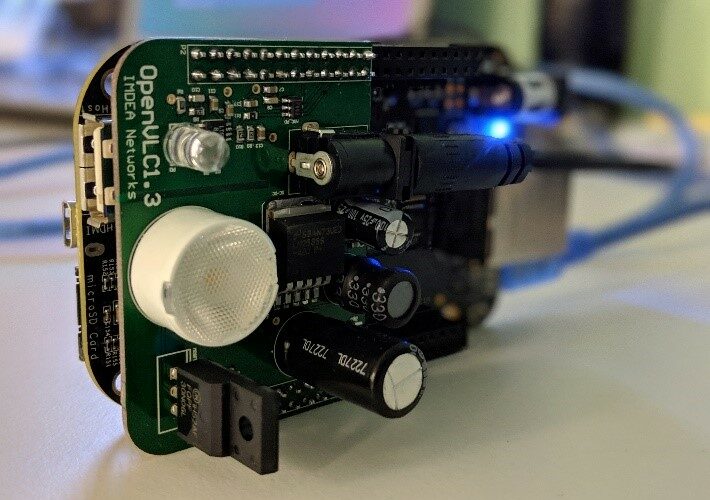
Read more arrow_right_altENLIGHT'EM: weaving the future of wireless communications with sustainable innovation
ENLIGHT’EM, an Innovative Training Networks project funded by a Marie Skłodowska-Curie Action, has ended in December 2023 marking a major...
Read more arrow_right_altWomen in STEM: Tianyue Chu
We interview our PhD Student Tianyue Chu on the occasion of International Day of Women and Girls in Science. She...
Read more arrow_right_altIMDEA Networks receives the visit of members of the Ministry for Digital Transformation
IMDEA Networks has received today the visit of prominent members of the Ministry for Digital Transformation and Civil Service. Present...
Read more arrow_right_altClaudio Fiandrino, awarded Ramón y Cajal research grant
IMDEA Networks Senior Researcher Claudio Fiandrino has been awarded the Ramón y Cajal grant from the Spanish Ministry of Science...
Read more arrow_right_alt“At IMDEA Networks you work with brilliant professors. It’s challenging but rewarding”
We interview one of the members of our Alumni Network, Dr. Santiago Andrés Azcoitia. He obtained his PhD from IMDEA...
Read more arrow_right_alt








Recent Comments